Microsoft patched this vulnerability a few months ago, but, if you haven’t updated your systems and backed up your data you should do so. Yesterday Microsoft issued patches for their old operating systems.
https://krebsonsecurity.com/2017/05/microsoft-issues-wanacrypt-patch-for-windows-8-xp/
This was done with a series of tools created by the NSA. Which have fallen into the wrong hands, obviously.
This really validates those people who say that we should encrypt and secure our devices, and that the government should never have a “back door” or “secret tool” or anything like that.
Anyway, I’m glad I only run Windows in virtual machines ![]() But I’ll update them anyway. Speaking of … Apparently this malware ‘checks’ to see if it’s in a virtual machine (i.e.: security researchers testing to see what it does) by trying to reach a made-up domain name. If it finds that domain name, it doesn’t activate…
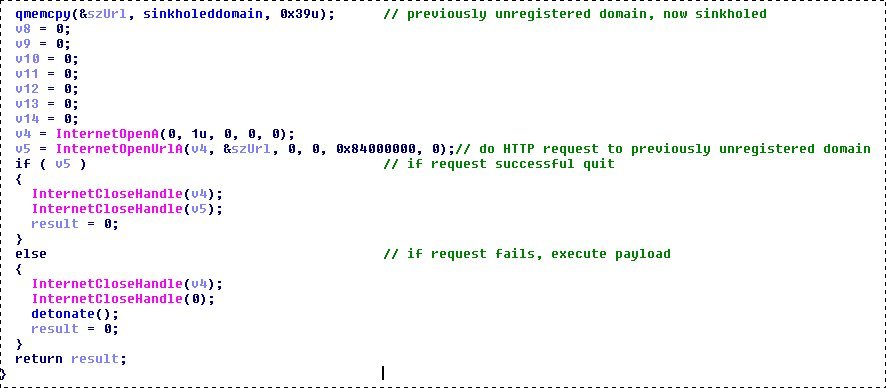
But I’ll update them anyway. Speaking of … Apparently this malware ‘checks’ to see if it’s in a virtual machine (i.e.: security researchers testing to see what it does) by trying to reach a made-up domain name. If it finds that domain name, it doesn’t activate…
And someone figured this out and registered that domain name. Which killed the malware ![]()
Just want to add… the best defence against ransomware isn’t a piece of software, or firewall, or whatever. Users are going to open attachments, or click on sketchy links no matter what you do.
The best defence against ransomware is to have a good backup.
And it’s good to have a backup anyway, just in case of hardware failure, fire, or mass evacuation, or whatever 
The rule I follow for backups is: 3 backups of important stuff. 2 different media / types of backup. And at least 1 off-site.
I use Crashplan and Backblaze for the really important stuff. With encrypted copies on Google Drive (unlimited space).
Out of the 9 computers at my place I have one Windows 10 Pro laptop. My 14 year old doesn’t like Linux. Haha. Good tips about backing up, thanks, MiG. ![]()
'Patch before Monday’
Although a temporary fix earlier slowed the infection rate, the attackers had now released a new version of the ransomware, he said.
Companies need to make sure they have updated their systems and “patched where they should” before staff arrived for work on Monday morning, the EU law enforcement agency head said.